Improving malware detection using multi‐view ensemble learning - Bai - 2016 - Security and Communication Networks - Wiley Online Library
Data Mining Classification Approaches for Malicious Executable File Detection - Document - Gale Academic OneFile
![PDF] Malicious Executables Detection Algorithm Research Based on Immune System Principles by Guo Zhen-he · 2374331249 · OA.mg PDF] Malicious Executables Detection Algorithm Research Based on Immune System Principles by Guo Zhen-he · 2374331249 · OA.mg](https://og.oa.mg/Malicious%20Executables%20Detection%20Algorithm%20Research%20Based%20on%20Immune%20System%20Principles.png?author=%20Guo%20Zhen-he)
PDF] Malicious Executables Detection Algorithm Research Based on Immune System Principles by Guo Zhen-he · 2374331249 · OA.mg

PPT – Data Mining for Security Applications: Detecting Malicious Executables PowerPoint presentation | free to view - id: 442827-MmMwZ
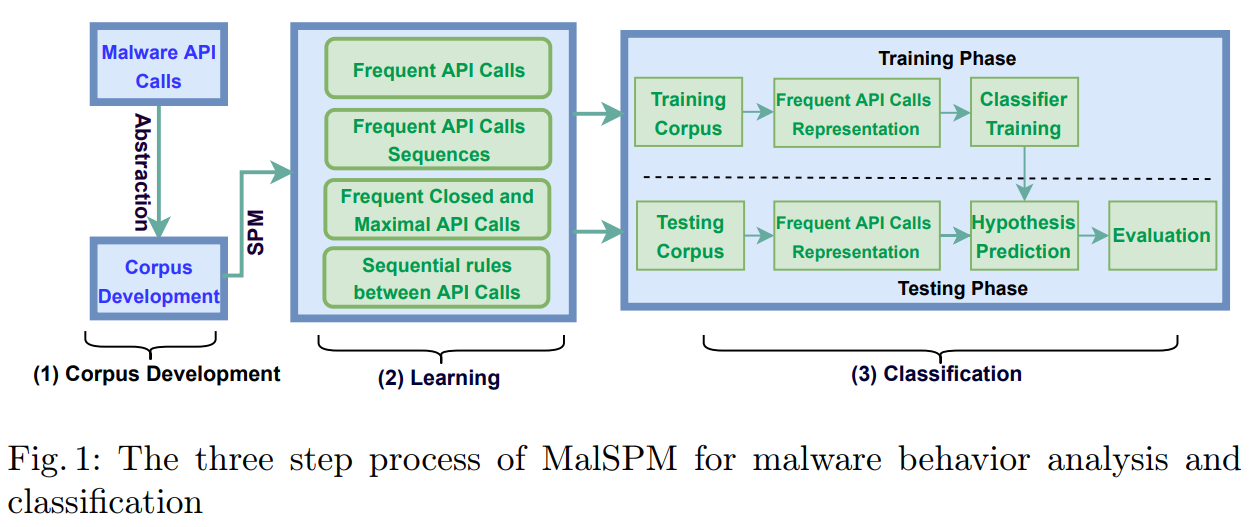
The Data Blog | A blog about data mining, data science, machine learning and big data, by Philippe Fournier-Viger | Page 4

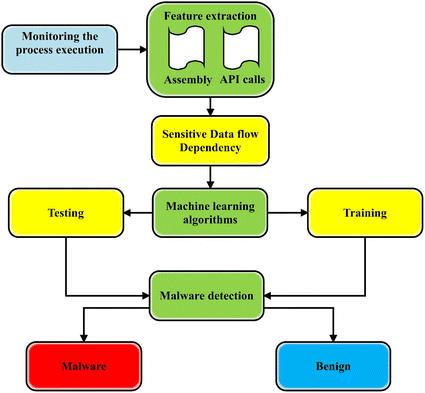
Shows the malware detection procedure of the proposed method: First... | Download Scientific Diagram
GitHub - shreyansh26/ELF-Miner: An implementation of the paper "ELF-Miner: Using Structural Knowledge and Data Mining Methods To Detect New (Linux) Malicious Executables"

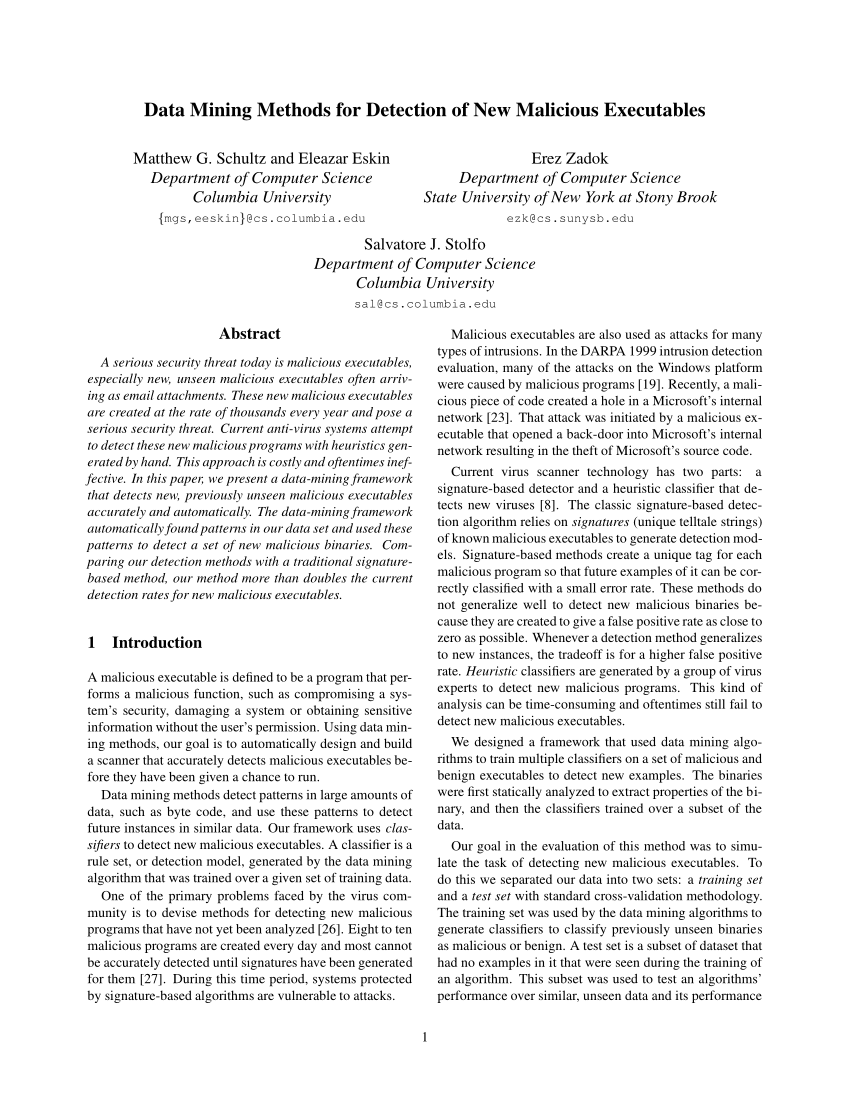
![PDF] Data mining methods for detection of new malicious executables | Semantic Scholar PDF] Data mining methods for detection of new malicious executables | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/31cfc6e2281426f4dd7325d73e105dc10bf5cdd5/9-Figure7-1.png)



![IJET-V1I2P2] Authors :Karishma Pandey, Madhura Naik, Junaid Qamar,Mahendra Patil IJET-V1I2P2] Authors :Karishma Pandey, Madhura Naik, Junaid Qamar,Mahendra Patil](https://cdn.slidesharecdn.com/ss_thumbnails/ijet-v1i2p2-150423020658-conversion-gate02-thumbnail.jpg?width=640&height=640&fit=bounds)

![PDF] Data mining methods for detection of new malicious executables | Semantic Scholar PDF] Data mining methods for detection of new malicious executables | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/31cfc6e2281426f4dd7325d73e105dc10bf5cdd5/9-Figure8-1.png)