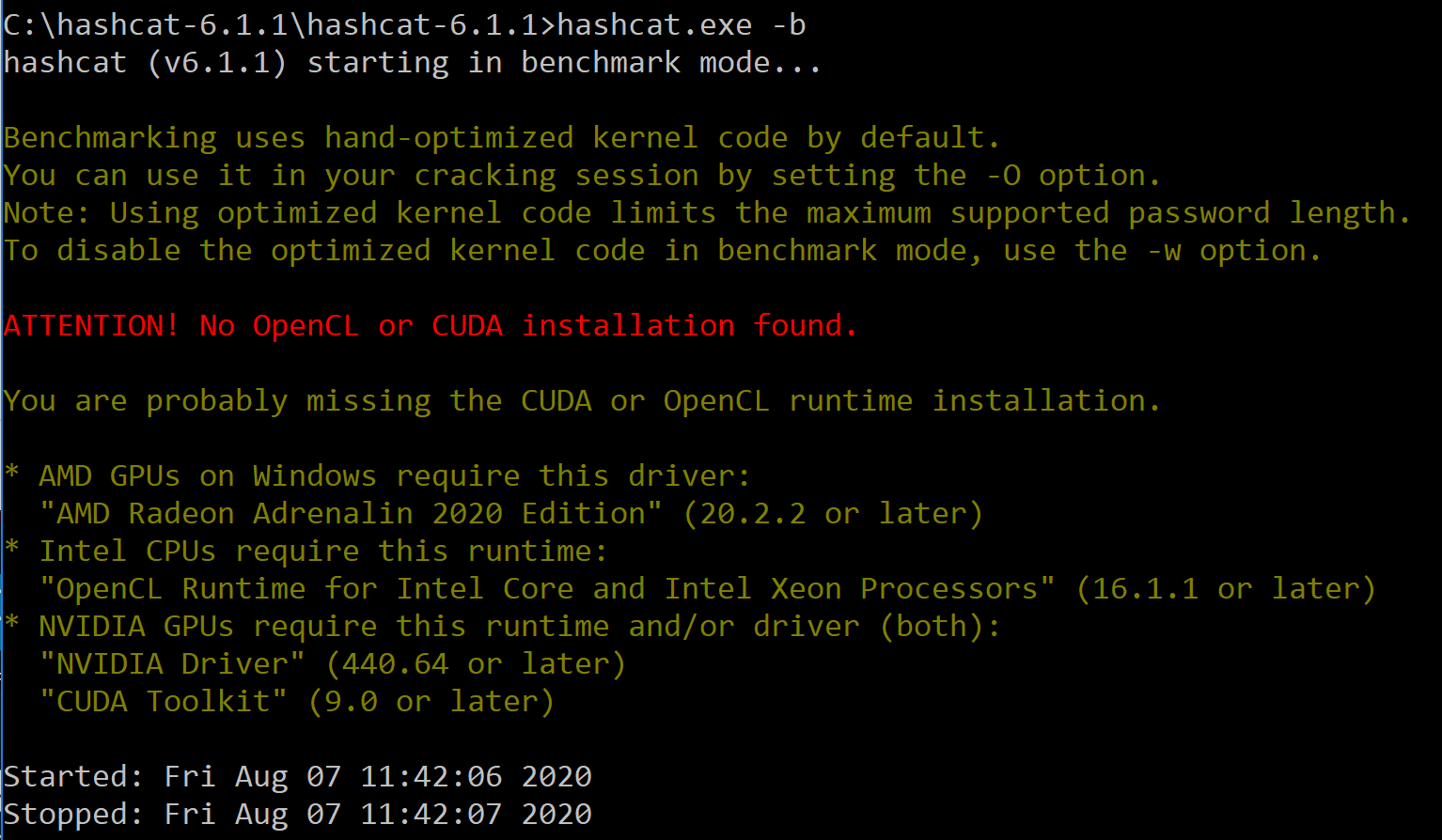
Elcomsoft vs. Hashcat Part 1: Hardware Acceleration, Supported Formats and Initial Configuration | ElcomSoft blog

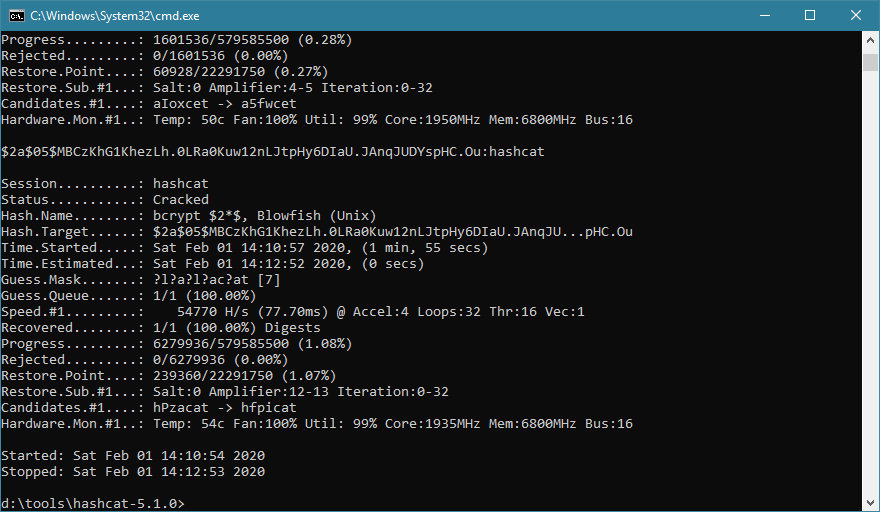
Screen capture of Hashcat running on GPU engine shown in Jigure 1 for... | Download Scientific Diagram

Chick3nman 🐔 on Twitter: "A SERIOUS @hashcat milestone has been reached! Here's a peek at the first ever single GPU server capable of benchmarking over 1.1MH/s Bcrypt. With 8x @NVIDIADC A100 PCI-E

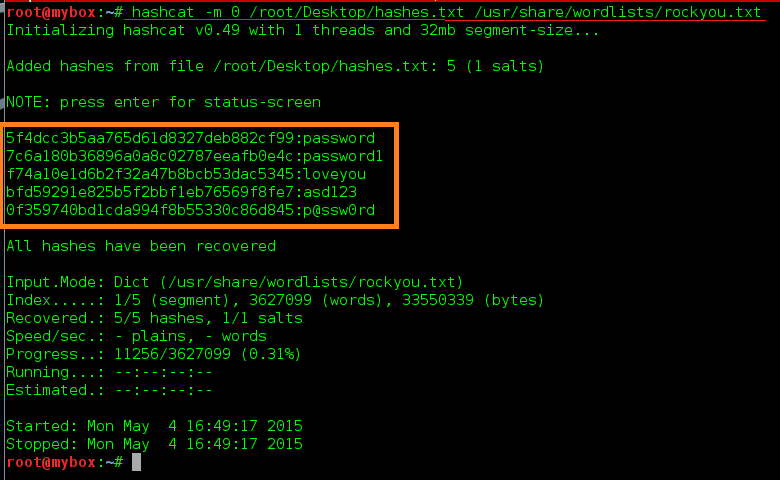
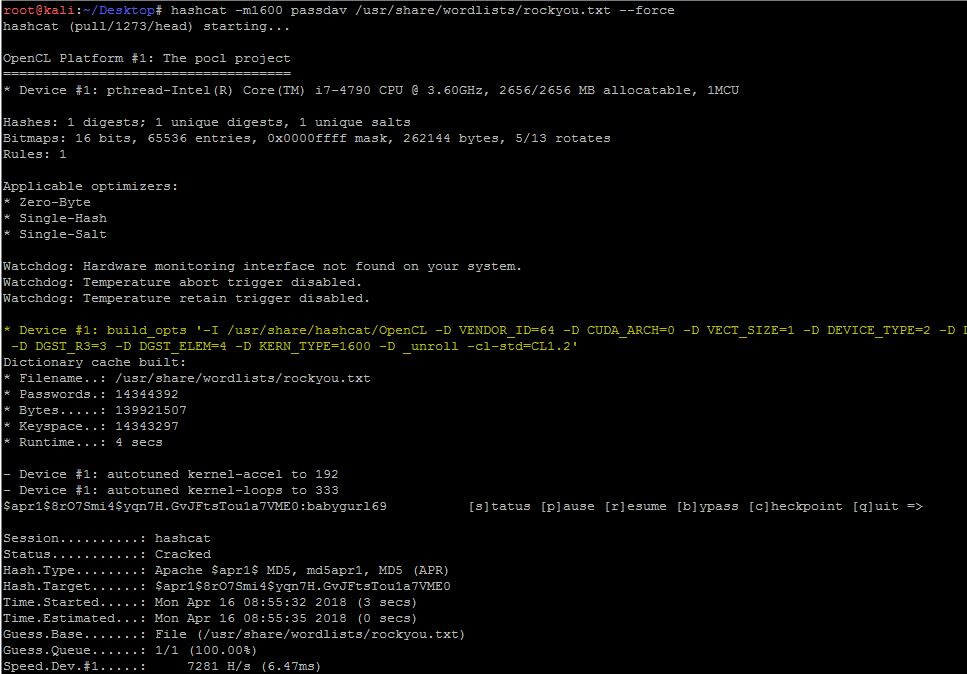
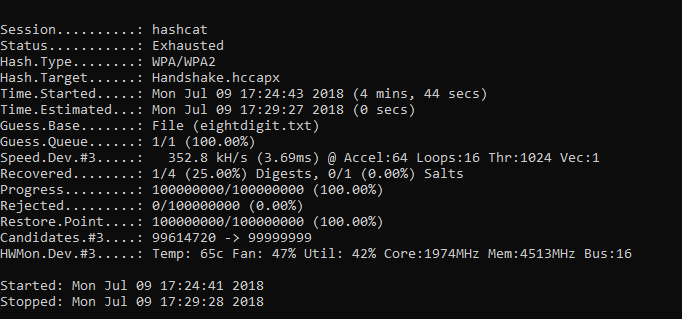
Ethical Hacking School - Cracking WPA2/WPA passwords using Hashcat in Kali Linux Hashcat, as a modest note the authors, this is the quickest tool for password recovery using the GPU. The program

![Using Hashcat - Web Penetration Testing with Kali Linux - Third Edition [Book] Using Hashcat - Web Penetration Testing with Kali Linux - Third Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781788623377/files/assets/827d5248-8803-4843-8424-3d1b7edbb124.png)



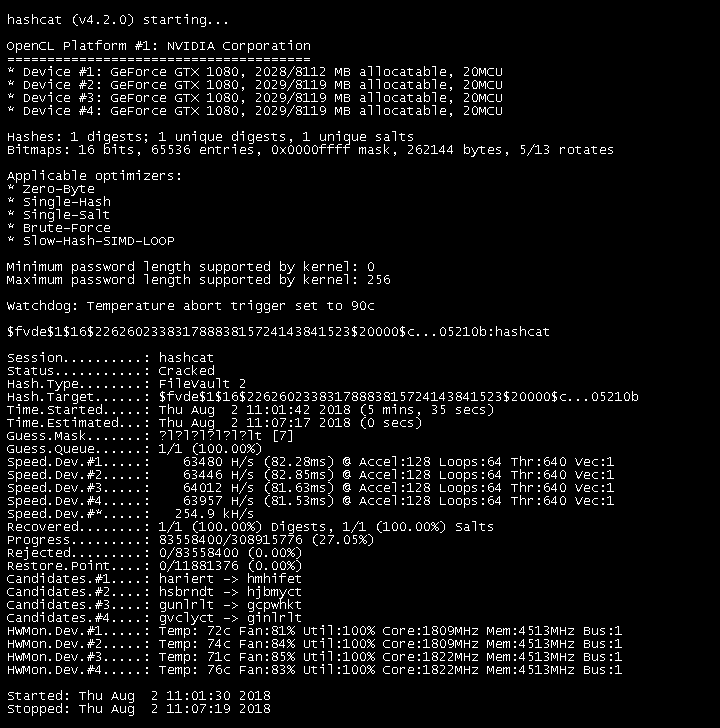





![Tested] oclHashcat 0.2.4 GPU-based Cracker: OpenCL / CUDA Test | Geeks3D Tested] oclHashcat 0.2.4 GPU-based Cracker: OpenCL / CUDA Test | Geeks3D](http://www.ozone3d.net/public/jegx/201101/oclHashcat_024_hd6970_single_gpu.jpg)
![Hashcat v0.46] Multi-Threaded Password Hash Cracking Tool Hashcat v0.46] Multi-Threaded Password Hash Cracking Tool](https://3.bp.blogspot.com/-ZbdkR2Q96BA/UoPxlGLn8PI/AAAAAAAABNg/CdvWcQF152w/s1600/hashcat.png)

